Content reviewed and updated: 01 March 2023
Table of Contents:
- What are the main types of business document within an organisation?
- What are the different types of ICT (Information Communication Technology) that are required for business document production?
- Why is it important to agree on the use, content, layout, quality standards, and deadlines for document production?
- What are document version control and authorisation, and why are they important?
- How might the requirements of security, data protection, copyright, and intellectual property legislation affect the production of business documents?
- How can I check the accuracy of a business document?
- How might the requirements of security, data protection, copyright, and IP legislation affect how business documents are stored and distributed?
- What are some examples of different channels for distribution?
- What types of information can be found in business organisations?
- Why should business information be stored safely and efficiently retrieved?
- What are the features of different types of information storage and retrieval systems?
- What are the legal requirements for storing business information?
What are the main types of business document within an organisation?
There are nine main types of business document that may be produced within an organisation. These are Business Letters, Emails, Reports, Lists, Instructions, Newsletters, Minutes of Meetings, Advertisements, and Numerical Information.
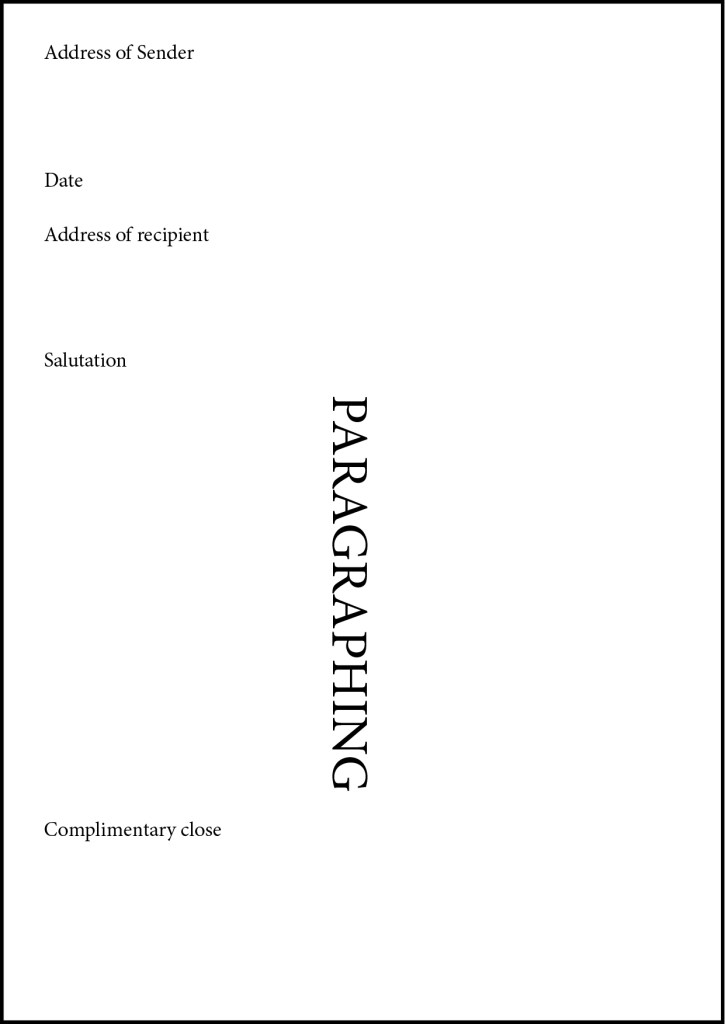
Business letters can be either formal or informal documents and are sent to specific recipients (usually external to a business) as a means of communicating. The format usually includes the name and address of the recipient, the name and address of the sender, a salutation and complimentary close, and paragraphing. (Figures 1 & 2)
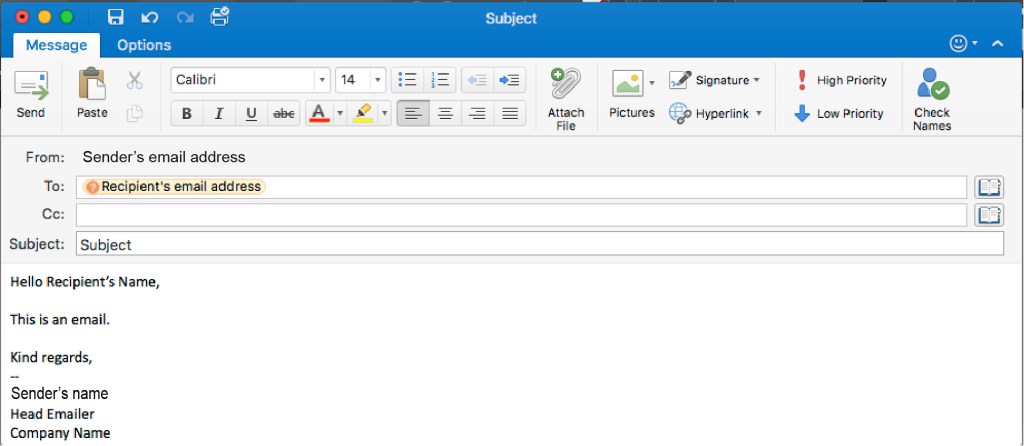
Emails are a means of communicating electronically, either within a business or without. The formatting of an email will often include the name and email address of the recipient, the name and email address of the sender, a subject, and a signature. (Figure 3)
Reports are written statements documenting what has been observed, heard, done, or investigated. The format of a report will often include a title, subheadings, a conclusion, findings, terms of reference, and recommendations. (Figure 7, 8)
Lists are documents with information ordered either numerically or alphabetically. For example, a list of tasks to be completed, or a list of items to be purchased.
Instructions are often similar to lists, but detail steps or rules to be followed. They are often listed either numerically or with bullet points, with short phrases in chronological order.
Newsletters are a means of keeping both employees and the wider public informed of happenings within the business. Their format will usually include columns of text and images. (Figure 6)
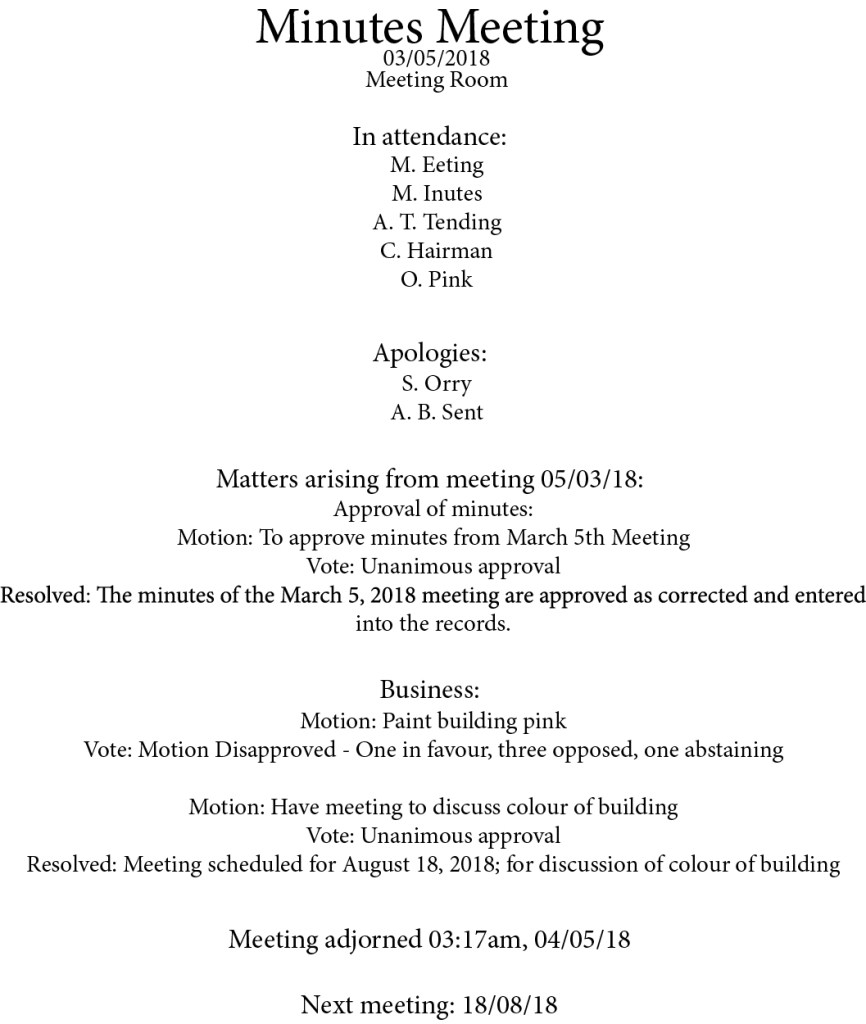
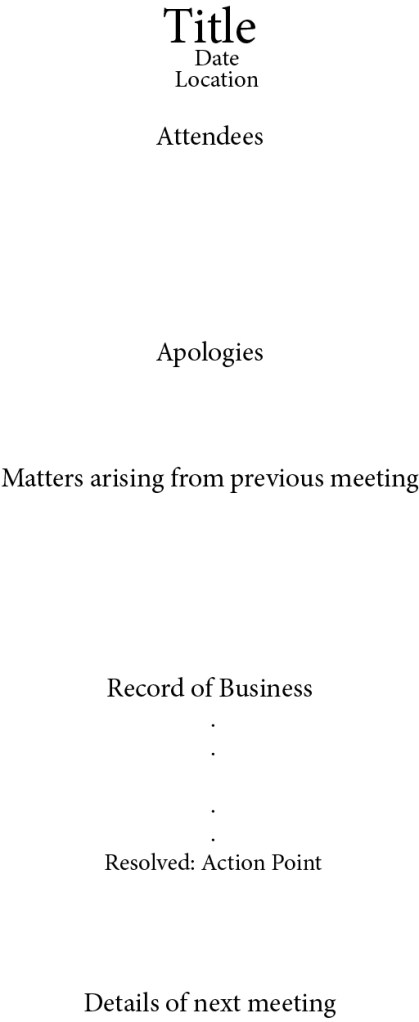
Minutes of Meetings are a formal record of a meeting that has taken place. The format of these will include a title, date, location, list of attendees, a notice of any apologies, matters arising from previous meetings, order of business, action points, and the details of the next meeting. (Figures 4 & 5)
Advertisements are part of the marketing of a business, and have no set format or style unless otherwise specified by an organisation’s “house style”
Finally, Numerical Information is data that can be presented in the form of tables, charts, and graphs. For example, records of spending, or details of the number of employees a business has.
What are the different types of ICT (Information Communication Technology) that are required for business document production?
To produce this wide range of business documents, many different pieces of ICT (Information Communication Technology) and software are required. These can be categorised as Word Processing software, Desktop Publishing software, Database software, Spreadsheet software, Presentation software, and Customised software.
Word Processing software is most suited for creating documents such as reports and business letters. This is because the software will usually only contain simple text-creation and editing features, such as spell-check functionality, and formatting settings for fonts, colours, and text alignment. An example of Word Processing software is Microsoft Word.
For more complicated and word-heavy documents, such as newsletters and advertisements, Desktop Publishing software like Adobe InDesign is most suitable. This software makes it easier to create layouts that are more complicated and to incorporate imagery. It will often contain considerably more complex functionality than basic word processors and allow a user to, for example, adjust typography and add decorative elements.
Database software is most equipped to aid in the storage and updating of data such as customer records, whereas Spreadsheet software (such as Microsoft Excel) is better for storing number-based data, such as financial records. This is because most spreadsheet software contains functionality that allows for complicated equations to be completed, whereas Database software is often bespoke and would contain ordering and search functionality.
“most spreadsheet software contains functionality that allows for complicated equations to be completed”
When a presentation is required, there is no better software to use than programs like Microsoft PowerPoint, which are created specifically for presentations. This type of software contains functionality for slides, custom timings, and other, subtler features that make it easy to create an attractive and functional presentation.
Finally, when a specific function is required that no software created for general use will allow, Customised (or bespoke) software can be created for specific organisational functions, such as payroll or phone directories. Database software, as mentioned above, is often customised.
Why is it important to agree on the use, content, layout, quality standards, and deadlines for document production?
Once the type of document has been established and the appropriate software selected, it is important to agree on the use, content, layout, quality standards, and deadlines of a document, for the reasons outlined below.
The first relates to agreeing on the use of a document, which covers factors such as a document’s security, storage, and distribution.
“agreeing on a document’s use ensures that the document adheres to regulatory requirements in light of GDPR“
A document’s usage can be outlined in a business’ protocol and guidelines, particularly in the case of security. Agreeing on the use determines who is authorised to see and read the document, where the document can be stored – and for how long – and covers any issue of confidentiality when it comes to data protection issues. It also concerns the distribution – can the document be published online? Are viewers allowed to share the document, and with whom? What licenses apply regarding sharing and “creative commons”? As such, agreeing on a document’s use ensures that the document adheres to regulatory requirements in light of GDPR and data protection legislation, and guarantees that information is not spread to the wrong people.
The next factor to consider and agree on is the content of the document. Agreeing on the content not only makes it clear exactly what the document is to cover and contain, but also clarifies what a document should not contain. If the content of a document is agreed upon and understood, the end result is more likely to meet expectations and serve its intended purpose. Agreeing on the content also ensures that the document follows both protocol and regulatory requirements when it comes to information sharing, along with copyright, intellectual property, and data protection legislation. There are also professional standards to consider – for example, some documents must contain slogans, or must not contain poor grammar or expletives. Those standards also tie in with ensuring that the document is appropriate for the intended audience in both its format and its tone.
“If the content of a document is agreed upon and understood, the end result is more likely to meet expectations and serve its intended purpose.”
To further ensure that a document is appropriate for its intended audience, factors regarding the layout of the document must be considered. A document’s ease of use can be affected by font size, the inclusion of imagery, or subheadings; each will be determined by the intended audience, whether the document is for a manager of another department or for the general public. The layout must also be suitable for the type of information contained and its purpose – for instance, a business letter usually provides information externally to an organisation, whereas a report is often created for internal information-sharing. The layout will often also be informed by the house style of an organisation. As an example, a particular font or certain imagery (such as a logo) may be required across all documents created on behalf of an organisation.
Agreeing on the quality standards of a document, as with the layout, also influences and is influenced by a document’s intended audience. A quick email notification sent across an organisation’s internal server will likely have far less strict quality standards than a newsletter sent to the stockholders of a business, and agreeing on these standards beforehand ensures that the document represents the company positively. Organisations will also often have a “house style”, as mentioned previously, which determines specific layout and formatting elements such as fonts or imagery. These house style guidelines will also affect the quality of the completed document, in addition to ensuring that there is consistency throughout all documents produced on behalf of the organisation.
“[house style] determines specific layout and formatting elements such as fonts or imagery.”
Finally, it is important to agree on the deadline for which a document must be completed. Agreeing on this ensures that the document is produced in plenty of time to serve its purpose as, if a deadline is not adequately communicated, the document could end up being rushed and therefore fail to meet professional standards. In the worst-case scenario, the document could be given a low priority due to the lack of a deadline, take too long to be completed, and become outdated or redundant before it has even been completed and distributed – thus failing to meet the needs of its intended audience or purpose.
What are document version control and authorisation, and why are they important?
Document version control and authorisation enable all of the above factors to be monitored and maintained, and make it easier for a business to adhere to data protection regulations.
Document version control consists of making a copy of a document each time it is edited, instead of overwriting the original, and assigning it a number or name that indicates how up-to-date the information contained within is. Doing so not only ensures that group collaboration on a document is easier, as it helps different users ensure that they are using the document that is the most correct and up-to-date, but also creates an audit trail that determines who made what change. This audit trail makes accountability for and correction of mistakes easier, as changes can often be tracked to a specific individual, and documents can be reverted to a previous version to void the mistake(s).
Authorisation further minimises the chance of inaccurate information being added or distributed. By limiting the number of individuals who have access to a document, the probability of a mistake is lowered, communication is easier (due to fewer collaborators), and accountability is greater for each authorised individual. Authorisation controls also include the locking of a document while it is being edited, so only the current editor can make changes. This reduces the chance of duplication of effort and ensures that only one version is being updated at a time, reducing confusion. Authorisation is also a vital factor in adhering to data protection regulations, and making sure that personal data is not leaked to those who are not supposed to have the information. By using authorisation controls like password protection to limit the number of people who can access a document, an organisation can almost guarantee that sensitive or confidential information does not fall into the wrong hands.
“Authorisation is also a vital factor in adhering to data protection regulations“
How might the requirements of security, data protection, copyright, and intellectual property legislation affect the production of business documents?
Adhering to those data protection regulations, along with other regulations enforced by Copyright, Intellectual Property, and general security legislation and protocols, can sometimes affect the production of business documents in a significant, often negative way. In these cases, it is much more important for production to be inconvenient than for production to be against regulatory requirements, or even against the law.
The requirements regarding document security often slow down production, due to the extra time that needs to be taken to implement encryption or password protection. In rarer cases, security regulations can halt production completely, particularly in cases of breaches in security. If a breach happens, the storage location of documents may need to be moved – for example, if a cloud storage site is hacked – and production must be halted for damage reduction to take place. The production of documents would cease while the source of the leak is investigated and preventative measures are developed and introduced.
Copyright requirements primarily concern gaining authorisation to use data or property that is owned by other individuals or companies. Copyright not only covers images, but also covers literary works, music/sound recordings, dramatic and artistic works (including film), and “typographical arrangements of published editions” (e.g. magazine layouts and content). Therefore, if a business document contains any of the above that is not created “in-house” and is sourced externally, it must seek permission for use from the owner of the copyright. This often means production will be halted while permission is sought and discussed, or delays can happen while alternatives are sought in case permission or license cannot be granted. The above is also true in the case of Intellectual Property, which is an umbrella term that covers copyright, as well as trademarks and patents. Nothing that is considered the Intellectual Property of an individual or company must be used without the permission of its owner, and the owner has the final say on how the property is used, edited, stored, and distributed. Additionally, if the property is created for the company by an external designer, that designer still owns the IP (unless otherwise discussed and agreed upon in a contract). This means production can again be delayed if, for example, an edit needs to be made and the designer is absent or out of contact.
“Copyright not only covers images, but also covers literary works, music/sound recordings, dramatic and artistic works (including film), and “typographical arrangements of published editions” (e.g. magazine layouts and content)”
Data Protection regulations tend to slow down production, as business protocols may dictate that authorisation from managers or individuals from other departments needs to be sought to use sensitive or personally identifiable information. This would mean that agreements from multiple parties must be received, and more individuals must be involved in the process – including the owner of the data in question. Thus, the production of business documents is slowed while authorisation is sought.
Another branch of Data Protection regulations is the requirement that all stored data must be kept accurate and up-to-date. Not only that, but keeping data used in business documents accurate is vital to shed a positive light on an organisation, avoid the consequences of spreading misinformation, and make the document seem professional. There are several ways to ensure a document is accurate, as outlined below.
How can I check the accuracy of a business document?
The first and fastest method is electronic spelling and grammar checks. While not completely infallible, these systems scan for misspellings and, in some cases, issues of poor grammar or syntax. These allow for a basic proofing of your document, at the very least.
“It is important to make sure that multiple reputable sources have shared the same information with the same context.”
The next most thorough way to ensure the accuracy of your document is to proofread a document yourself, once it is completed. This means reading through the entire document and keeping an eye out for errors that an electronic spellcheck may have missed. For example, while the spellcheck can tell you if you have spelt “they’re” wrong, it won’t always correct you on the form of their/they’re/there to use. So if you have used the wrong “they’re”, theirs not always any indication. As an extra layer of proofing, it’s best to ask an authorised person to proofread your document, too, for an objective viewpoint.
If you are editing or updating a document created previously, sending drafts to the originator of the document is an effective way to check the accuracy, in case the original point, purpose, or precision of the document has been distorted through newer amendments.
Finally, if you are using numerical data from a secondary source, repeating your research to confirm the data is important to ensure that the figures included are correct. This extra confirmation also ensures that the figures have not been changed, revised, or updated since the last time they were checked. In a similar vein, if you have any non-numerical information (such as information from a study posted on the Internet), it is important to cross-reference with at least one other objective source that is entirely unrelated to the first, to avoid using biased or “fake” information. Particularly in the case of the Internet, figures, statistics, and general information can be distorted or taken out of context to fit a particular bias. As such, it is important to make sure that multiple reputable sources have shared the same information with the same context.
How might the requirements of security, data protection, copyright, and IP legislation affect how business documents are stored and distributed?
Just as a range of regulatory requirements and legislation affects the production of business documents, these regulations also affect how documents are stored and distributed within an organisation.
The first factor that affects the storage and distribution of business documents is security. In the case of storage, security regulations may dictate where hard-copy documents may be stored or archived, such as within areas where only authorised individuals are given access via key cards or coded locks. The same regulations may also affect which sites or devices electronic documents are stored or archived on. In addition, they could also affect the naming protocols for identifying stored documents, so that files can only be found with the correct search criteria or code. As for distribution, security protocols often also dictate that electronic files can only be transferred via secure sites – such as password-protected storage sites and emails within a secure network. Often, hard-copy documents must be distributed with secure postal services, such as private couriers or special Post Office services.
Another set of regulations that affect the storage and distribution of business documents is Data Protection legislation, particularly GDPR. According to these regulations, sensitive or personal data must be stored with access restricted to all but those authorised to view it. In addition, data may only be stored for either the duration specified by the owner of the data or the duration agreed upon at the point of collection, with informed consent. As for the distribution of said documents, confidential documents must only be shared with authorised recipients and, when distributing internationally, international regulatory requirements must be followed.
“The copyright owner has the final say on where and to what extent their material can be distributed.”
Copyright legislation, or the Copyright, Designs, and Patents Act 1988, only affects the storage and distribution of business documents if they contain the works of others under the following criteria: artistic, literary, music, sound recording, film, dramatic, or typographical arrangement of published editions. In these cases, the storage of the documents can only be maintained for the duration specified by the copyright owner, if at all, and copyrighted materials must be clearly indicated and declared when distributing a document. An example of this would be the use of a copyrighted image in a newspaper, in which case there is often a caption underneath with both a description and a credit/note identifying the copyright owner. Additionally, the copyright owner has the final say on where and to what extent their material can be distributed.
As before, the legislation for Intellectual Property is very similar to that of Copyright, in that documents using another’s Intellectual Property (e.g. trademarks) can only be stored for the time specified by the owner, must be declared when distributing, and deletion of the property must be immediate upon the request of the owner.
What are some examples of different channels for distribution?
To distribute business documents, two primary channels can be used; these can be characterised as electronic and hard-copy. Electronic channels – emails, for example – have benefits in that multiple recipients can be specified and delivered to instantly, files can be added as attachments, password-protection features are available, and most email systems require a username and password for access to be granted to emails. Additionally, the names and email addresses of recipients can be hidden from the other recipients, using the “Bcc:” functionality – in accordance with GDPR.
Hard-copy or paper channels, on the other hand, are not always as secure and instantaneous but are the best option in some circumstances. These methods, such as internal pigeonhole systems or Post Office systems, enable an organisation to distribute documents that require manual sign-off. There is no cost for internal distribution systems, and there is a range of Post Office services that offer specific delivery conditions for any type of document (such as courier services or tracked delivery).
What types of information can be found in business organisations?
Different types of information require different methods of distribution, so it is important to understand the types of information commonly found in business organisations. These types can be broken down as follows: Customer Records, Financial Records, Staff Records, Correspondence, Statistical Information, Records of service organisations/suppliers, policies, and procedures.
Organisations store a wide range of records relating to customers, staff, finances, and suppliers. These can range from basic anonymous statistical data to sensitive personal data that is regulated by GDPR. Customer records are records of any individual or organisation that has received products or services from the organisation and would contain personally identifiable information.
Financial records are details of all financial activity by the company, including profits, losses, and budgets.
Staff records usually include banking details for wages, details of emergency contacts, and home addresses for tax reasons or other legal requirements, and will be subject to GDPR. Finally, an organisation will often also keep records of any service organisations/suppliers from whom they have received a product or service.
The other types of information – correspondence, statistical information, policies, and procedures – are less likely to fall under data protection regulations, but are still important to retain for the running of an organisation.
Correspondence refers to written communication, such as emails, that has been sent or received either internally or externally to an organisation. These will often be stored for future reference purposes, for example as a reminder of a meeting, or as a paper trail for accountability.
An example of Statistical information would be data from an organisation’s marketing department, where tracking of demographics or engagement on social media takes place. Statistical data can be defined as information that can be collected, organised, and analysed.
Policies refer to guidelines, set either by the government or by the organisation, which act as aids in decision-making and procedures. These can be, for example, health and safety policies, or dress code policies. Procedures are in a similar vein but can be considered as instructions for how to handle certain situations, in case a policy has been violated. For example, many organisations will have disciplinary procedures that all members of staff are made aware of, in case of a policy or protocol violation.
Why should business information be stored safely and efficiently retrieved?
When so much information is present within an organisation, the safe storage and efficient retrieval of information is crucial if an organisation is to remain lawful and ethical. If the method of storage that an organisation uses is secure, breaches and leaks of personal data are unlikely, and the organisation is less likely to be fined or sued for negligence. If strict and universal care is taken in the security of data, the company will find it easier to comply with all current and future Data Protection regulations.
“If information is easy to locate and retrieve, it is far easier to adhere to [GDPR] and continue to avoid monetary reparation.”
Additionally, processes that ensure the efficient retrieval of information are further key steps that can be taken concerning Data Protection. The current GDPR dictates that data can only be stored for the duration agreed by the data owner, and this data owner can request the retrieval or deletion of said data at any time, and the organisation must comply with immediate effect. If information is easy to locate and retrieve, it is far easier to adhere to these regulations and continue to avoid monetary reparation.
Processes that ensure the efficient retrieval of information also save time and effort for any authorised employee that requires said data. If information is easy to obtain, the task(s) that require said information can be completed faster, allowing for better productivity.
What are the features of different types of information storage and retrieval systems?
When it comes to storing and retrieving data, there is a range of systems an organisation can use. In both cases, these can be categorised under electronic and hard-copy systems.
For storage, the electronic systems that can be used include cloud/drive storage (such as Google Drive), USB drive storage, and company networks (shared network drives). In all those examples, there are methods of encryption and/or authorisation controls that can be initiated to protect sensitive data, and information can often be duplicated and distributed instantly.
Hard-copy storage systems involve on-site and off-site archiving, such as filing in areas that can only be accessed by authorised persons. There may be fewer options for restricting access via hard copy than via electronic, but there are also fewer ways a data breach can happen (as information has to be physically stolen or misplaced).
For the retrieval of information, electronic systems often offer convenient and prompt methods – such as file-naming functionality that allows for more effective and accurate search functions. If a business has solid file-naming protocols in place, anyone searching for a specific file will know what search criteria to use. There are also methods of retrieval that may not be faster but are more secure, such as using passwords and sign-in sign-out features that enforce strict authorisation policies. Hard-copy systems for retrieval, much like hard-copy storage methods, are often slower and more cumbersome to retrieve information from. However, using systems such as alphabetical or numerical filing systems makes retrieval of specific information easier – as long as you know what you’re looking for.
What are the legal requirements for storing business information?
As mentioned previously, business information (particularly personal or sensitive information) is subject to strict regulations enforced by GDPR and data protection guidelines, and the storage of said information is no different. Data Protection legislation dictates that data should be a) only stored for the duration permitted by the data controller and/or the data’s owner, b) accessible to authorised individuals only, and c) regularly updated to maintain accuracy.
Additionally, some regulations apply to the storage of financial information, too. These requirements dictate that, like sensitive data, financial data should only be accessible to authorised personnel. It is also similar to data protection laws in that this data should only be stored for the permitted time – although guidelines regarding these limits are provided. For accounts, the limit is 7 years, and for personnel, the limit is 50 years.
If an organisation understands and adheres to all of the above, it can avoid fines and legal action regarding business document production and information management for the duration of its existence.



This essay covers the topics:
DESCRIBE DIFFERENT TYPES OF BUSINESS DOCUMENTS THAT MAY BE PRODUCED AND THE FORMAT TO BE FOLLOWED FOR EACH.
EXPLAIN THE USE OF DIFFERENT TYPES OF INFORMATION COMMUNICATION TECHNOLOGY (ICT) FOR DOCUMENT PRODUCTION.
EXPLAIN THE REASONS FOR AGREEING THE USE, CONTENT, LAYOUT, QUALITY STANDARDS, AND DEADLINES FOR DOCUMENT PRODUCTION.
EXPLAIN THE IMPORTANCE OF DOCUMENT VERSION CONTROL AND AUTHORISATION.
EXPLAIN HOW THE REQUIREMENTS OF SECURITY, DATA PROTECTION, COPYRIGHT, AND INTELLECTUAL PROPERTY LEGISLATION MAY AFFECT THE PRODUCTION OF BUSINESS DOCUMENTS.
EXPLAIN HOW TO CHECK THE ACCURACY OF BUSINESS DOCUMENTS
EXPLAIN HOW THE REQUIREMENTS OF SECURITY, DATA PROTECTION, COPYRIGHT, AND INTELLECTUAL PROPERTY LEGISLATION MAY AFFECT THE DISTRIBUTION AND STORAGE OF BUSINESS DOCUMENTS.
DESCRIBE DIFFERENT TYPES OF DISTRIBUTION CHANNELS.
DESCRIBE THE TYPES OF INFORMATION FOUND IN BUSINESS ORGANISATIONS.
EXPLAIN THE NEED FOR SAFE STORAGE AND EFFICIENT RETRIEVAL OF INFORMATION.
DESCRIBE THE FEATURES OF DIFFERENT TYPES OF SYSTEMS USED FOR STORAGE AND RETRIEVAL OF INFORMATION.
DESCRIBE THE LEGAL REQUIREMENTS FOR STORING BUSINESS INFORMATION.


Leave a comment